AES256GCM 10G25G IP Core Datasheet

Core Facts |
|
|
Provided with Core |
|
|
Documentation |
User Guide, Design Guide |
|
Design File Formats |
Encrypted File |
|
Instantiation Templates |
VHDL |
|
Reference Designs & Application Notes |
Vivado Project, See Reference design manual |
|
Additional Items |
Demo on ZCU106 |
|
Support |
|
|
Support Provided by Design Gateway Co., Ltd. |
|
Design Gateway Co.,Ltd
E-mail: ip-sales@design-gateway.com
URL: design-gateway.com
Features
· Support AES-GCM mode standard.
· Support 256-bit key size, 96-bit iv size.
· Support zero-length AAD or data input.
· Peak throughput rate at 128 Mbits/MHz.
· Speed up to 38.4 Gbps @300MHz.
Table 1: Example Implementation Statistics (UltraScale+)
|
Family |
Example Device |
Fmax (MHz) |
CLB Regs |
CLB LUTs |
CLB1 |
IOB |
BRAMTile |
Design Tools |
|
Zynq-Ultrascale+ |
xczu7ev-ffvc1156-2-e |
300 |
4822 |
16325 |
3108 |
- |
- |
Vivado2021.1 |
|
Kintex-UltraScale+2 |
xcku5p-ffvb676-2-e |
300 |
4822 |
16283 |
3186 |
- |
- |
Vivado2021.1 |
|
Virtex-Ultrascale+2 |
xcvu9p-flga2104-2L-e |
325 |
4822 |
16307 |
3269 |
- |
- |
Vivado2021.1 |
Table 2: Example Implementation Statistics (Versal)
|
Example Device |
Fmax (MHz) |
CLB Regs |
CLB LUTs |
Slice1 |
IOB |
BRAMTile |
Design Tools |
|
|
Versal AI Core2 |
xcvc1902-vsva2197-2MP-e-S |
275 |
4821 |
17846 |
3097 |
- |
- |
Vivado2021.1 |
Notes:
1) Actual logic resource dependent on percentage of unrelated logic
2) The results were obtained from implementation in the same environment, but have not been tested on the actual board.
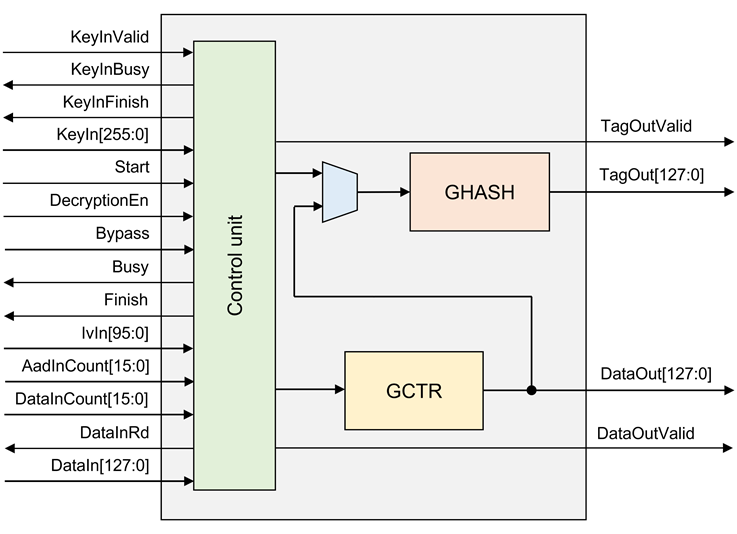
Figure 1: Block Diagram
General Description
AES256-GCM-10G25G IP Core (AES256GCM10G25GIP) implement the advanced encryption standard (AES) with 256-bit key in Galois/Counter Mode (GCM) which is widely used for Authenticated Encryption with Associated Data (AEAD) application, including IPSEC, MACSEC and TLS (Transport Layer Security) versions 1.2 and 1.3. Additionally, AES-GCM is used in fiber channel communications and storage applications.
AES256GCM10G25GIP works with 256-bit AES-key and 96-bit Initialization Vector (IV). It can provide confidentiality and data authentication by using Additional Authenticated Data (AAD) and authentication tag. It is designed to support zero-length plaintext/ciphertext input which is the special case of GCM mode, called GMAC, and also support zero-length AAD.
There are 2 main operations in AES-GCM, AES encryption/decryption by GCTR and tag calculation by GHASH algorithm. AES256GCM10G25GIP can operate 128-bit data every clock cycle, as a result, it can operate at speeds up to 38.4Gbps at 300MHz, which can be used effectively on 10G/25G Ethernet.
Functional Description
AES256GCM10G25G interface signals can be divided into 3 parts, i.e., Key setting signals, parameter setting signals and data control signals.
Table 3: Interface signals of AES256GCM10G25GIP
|
Signal name |
Dir |
Description |
|
RstB |
In |
IP core system reset. Active low. |
|
Clk |
In |
IP core system clock. |
|
version[31:0] |
Out |
32-bit version number of AES256GCM10G25GIP. |
|
Key setting signals |
||
|
KeyInValid |
In |
KeyInValid is a user signal to specify data valid of KeyIn. Assert to ‘1’ to set up KeyIn into AES256GCM10G25GIP. |
|
KeyInBusy |
Out |
KeyInBusy specifies busy status of Key setting. Assert to ‘1’ after user set KeyInValid, until the last cycle of operation. KeyInValid or Start will be ignored while KeyInBusy is ‘1’.
|
|
KeyInFinish |
Out |
KeyInFinish specifies finish status of Key setting. Assert to ‘1’ at the last cycle of operation.
|
|
KeyIn[255:0] |
In |
KeyIn is 256-bit key data for AES block cipher in CTR mode of operation. KeyIn must be valid when KeyInValid is asserted to ‘1’.
|
|
Parameter setting signals |
||
|
Start |
In |
Start is a user signal to start AES256GCM10G25GIP operation. |
|
DecryptionEn |
In |
DecryptionEn is a user signal to specify mode of operation. DecryptionEn=‘0’ for encryption, DecryptionEn=‘1’ for decryption. DecryptionEn must be valid during operation. |
|
Bypass |
In |
Bypass is a user signal to specify bypass mode of operation. Bypass=‘0’ for encryption/decryption mode, Bypass=‘1’ for bypass mode. Bypass must be valid during operation.
|
|
Busy |
Out |
Busy specifies busy status of operation. Busy is active after user set Start, until operation is done. KeyInValid or Start will be ignored while Busy is ‘1’.
|
|
Finish |
Out |
Finish specifies finish status of AES256GCM10G25GIP. Assert to ‘1’ at the last cycle of operation.
|
|
IvIn[95:0] |
In |
IvIn is 96-bit IV data for AES block cipher in CTR mode of operation. IvIn must be valid during operation. |
|
AadInCount[15:0] |
In |
AadInCount is the number of AAD in byte. AadInCount must be valid during operation. |
|
DataInCount[15:0] |
In |
DataInCount is the number of input data in byte. DataInCount must be valid during operation. |
|
Data control signals |
||
|
DataInRd |
Out |
DataInRd is a control signal to read DataIn. |
|
DataIn[127:0] |
In |
DataIn is 128-bit input data, both of AAD and data. DataIn must be valid when DataInRd is asserted to ‘1’. |
|
DataOutValid |
Out |
DataOutValid specifies data valid for DataOut. Assert to ‘1’ when cipher data is valid for encryption mode or plain data is valid for decryption mode. |
|
DataOut[127:0] |
Out |
DataOut is 128-bit data output of AES256GCM10G25GIP. Valid when DataOutValid is asserted to ‘1’. |
|
TagOutValid |
Out |
TagOutValid specifies tag valid. Assert to ‘1’ when tag calculation is done. |
|
TagOut[127:0] |
Out |
TagOut is 128-bit tag output of AES256GCM10G25GIP. Valid when TagOutValid is asserted to ‘1’. |
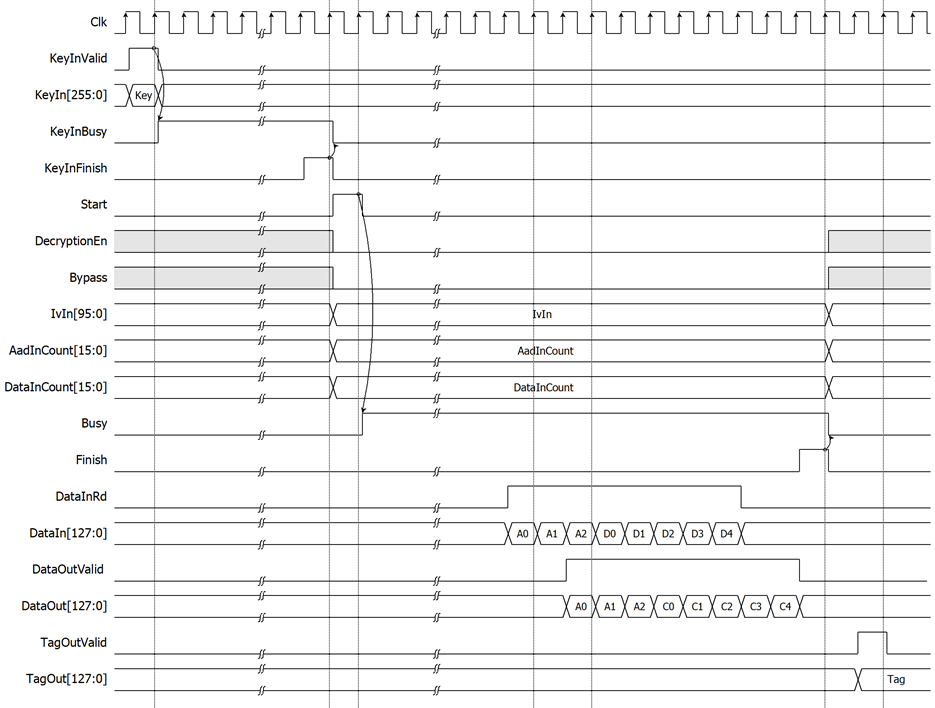
Figure 2: AES256GCM10G25G timing diagram in encryption mode
AES256GCM10G25G operation is as simple as 3 steps to use as below.
1. Key setting
Key setting is the first step to use AES256GCM10G25G. As shown in Figure 2, AES256GCM10G25G is started key setting process when KeyInValid=‘1’. KeyInBusy is set to be ‘1’ in the next cycle. KeyInFinish is active only one clock at the last cycle of process and KeyInBusy is cleared to ‘0’ in the next cycle. After that, this KeyIn is used for every process and can be changed via KeyInValid is asserted to ‘1’.
2. Parameter setting
After key setting, AES256GCM10G25G starts the process when Start is asserted to ‘1’. DecryptionEn, Bypass, KeyIn, IvIn, AadInCount and DataInCount must be valid when Start=‘1’ and be hold during operation. User can set DecryptionEn to ‘0’ and Bypass to ‘0’ for operating in encryption mode as shown in Figure 2 or set DecryptionEn to ‘1’ and Bypass to ‘0’ for operating in decryption mode as shown in Figure 3. And set Bypass to ‘1’ for operating in Bypass mode as shown in Figure 4.
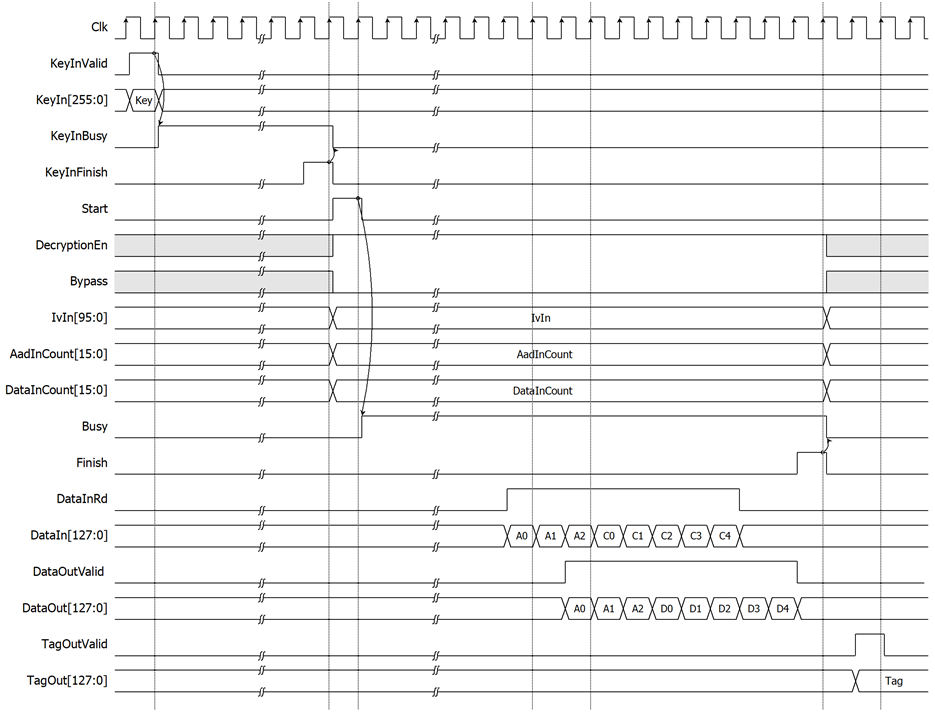
Figure 3: AES256GCM10G25G timing diagram in decryption mode
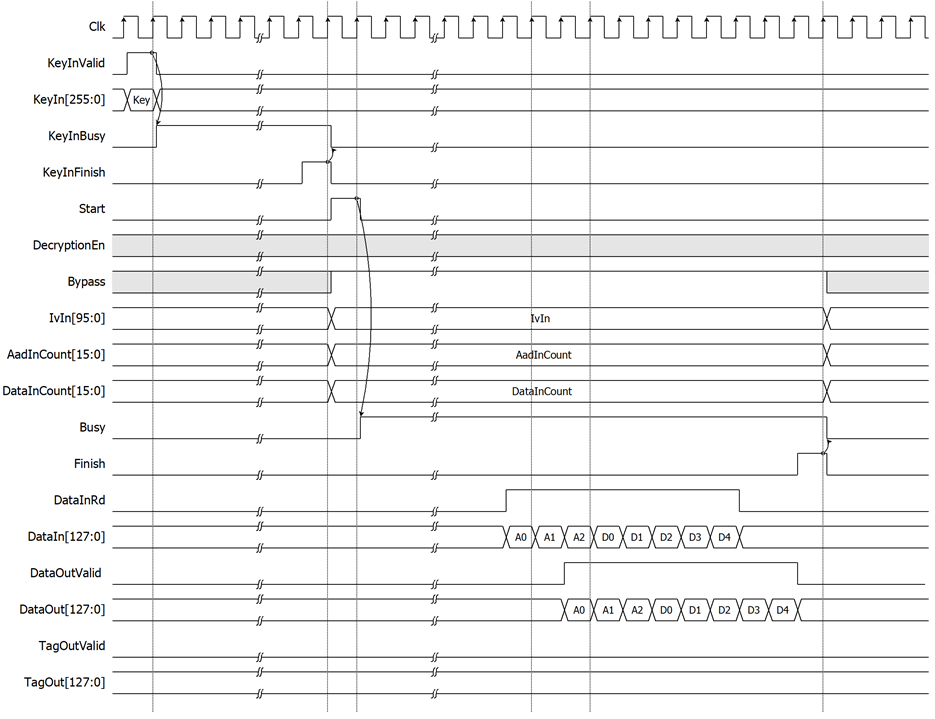
Figure 4: AES256GCM10G25G timing diagram in Bypass mode
For the best performance of process, Figure 5 shows the timing diagram of continuous and pipelining process. User can use Finish signal as a trigger signal for setting new parameters and sending new start command in next cycle.
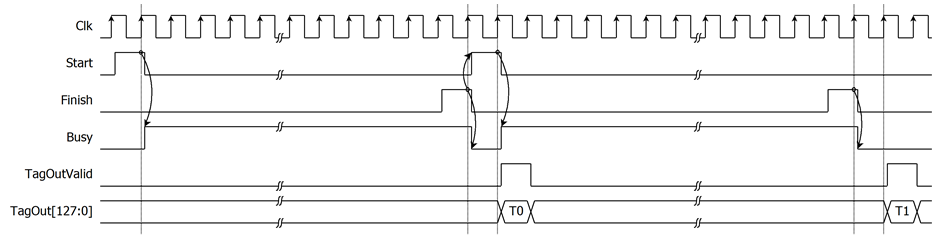
Figure 5: Continuous and pipelining operation
3. Data control
According to DataIn width is 128 bits (16 bytes) and AES256GCM10G25G is designed to read DataIn every clock cycle when AES256GCM10G25G is ready to start encryption/decryption process. After Start is set to begin the operation, user must prepare first valid DataIn[127:0]. Then user can use DataInRd signal as a trigger signal for setting the next DataIn continuously. If AadInCount is not aligned to 128 bits (16 bytes), the last 128-bit AAD must be right-padded with zeros.
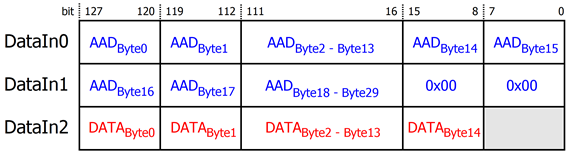
Figure 6: DataIn arrangement for 30-byte AAD and 15-byte data
Figure 6 is a detailed example of 30-byte AAD and 15-byte data preparation. DataIn0, DataIn1 and DataIn2 is represent as DataIn[127:0] in the first, second and third clock cycle respectively. The first 16-byte of AAD (AADBytes0-AADBytes15) is set as DataIn0[127:120], ..., DataIn0[7:0]. The remained 14-byte of AAD (AADBytes16-AADBytes29) is set as DataIn1[127:120], ..., DataIn1[23:16] and DataIn1[15:0] must be zeros. Then the remained 15-byte data (DATABytes0-DATABytes14) must be set as DataIn2[127:8].
As shown in Figure 2 and Figure 3, at last operation cycle, the Finish signal is asserted to ‘1’ and Busy signal is cleared to ‘0’ in the next cycle. TagOutValid is active only one clock on the next clock after Busy is cleared to ‘0’. In case of Bypass mode is active as shown in Figure 4, the TagOut is not calculated and TagOutValid is not active.
Verification Methods
AES256-GCM-10G25G IP functionality were verified on real board design by using ZCU106 Evaluation Board.
Recommended Design Experience
The user must be familiar with HDL design methodology to integrate this IP into system.
Ordering Information
This product is available directly from Design Gateway Co., Ltd. Please contact Design Gateway Co., Ltd. For pricing and additional information about this product using the contact information on the front page of this datasheet.
Revision History
|
Revision |
Date |
Description |
|
1.00 |
21/Jun/2022 |
New release |
|
1.02 |
20/Sep/2022 |
New design to improve performance |
|
1.03 |
27/Sep/2022 |
Update pictures and description |
|
1.04 |
23/Feb/2023 |
- Add Bypass feature - Improve performance - Add more resource information. |