Rev1.00 2-Jun-2023
4 Command detail and testing result
4.3 Set encryption/decryption IV
This document describes the instruction to demonstrate the operation of AES256XTSIP on ZCU106 Evaluation Board. In the demonstration, AES256XTSIP are used to encrypt and decrypt data between two memories in FPGA. User can fill memory with plain or cipher data patterns, set encryption key, tweakable key, Initialization Vector (IV) and control test operation via serial console.
1 Environment Setup
To operate AES256XTSIP demo, please prepare following test environment.
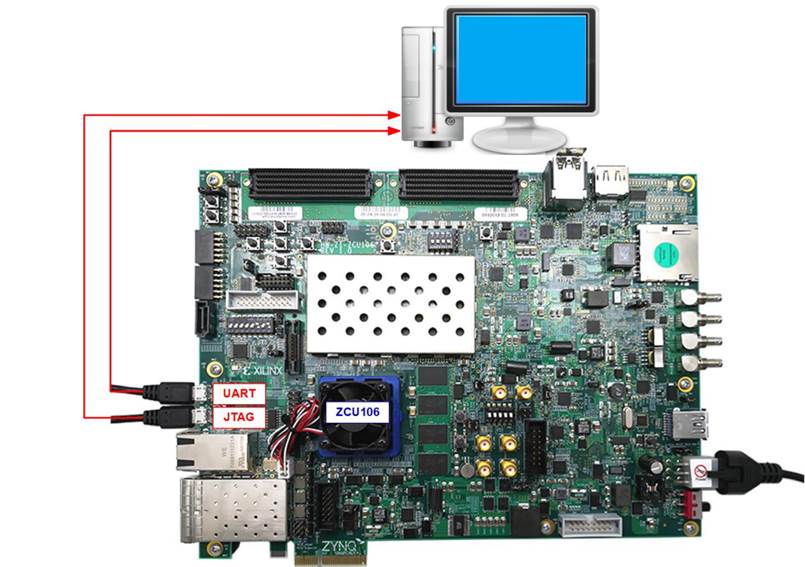
1) FPGA development boards (ZCU106 board).
2) Test PC.
3) Micro USB cable for JTAG connection connecting between ZCU106 board and Test PC.
4) Micro USB cable for UART connection connecting between ZCU106 board and Test PC.
5) Vivado tool for programming FPGA installed on Test PC.
6) Serial console software such as TeraTerm installed on PC. The setting on the console is
7) Baudrate=115200, Data=8-bit, Non-parity and Stop=1.
8) Batch file named “AES256XTSIPTest_ZCU106.bat” (To download these files, please visit our web site at www.design-gateway.com)
Figure 1‑1 AES256XTSIP demo environment on ZCU106 board
2 ZCU106 board setup
1) Make sure power switch is off and connect power supply to FPGA development board.
2) Connect two USB cables between FPGA board and PC via micro-USB ports.
3) Power on system.
4) Download configuration file and firmware to FPGA board by following step,
a) open Vivado TCL shell.
b) change current directory to download folder which includes demo configuration file.
c) Type “AES256XTSIPTest_ZCU106.bat”, as shown in Figure 2-1.
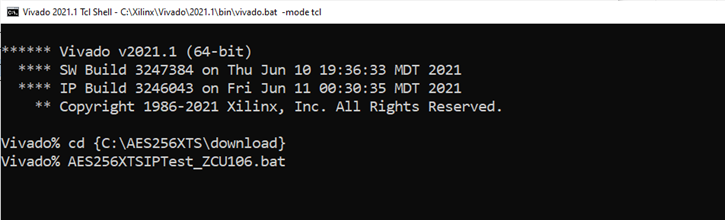
Figure 2‑1 Example command script for download configuration file
3 Serial Console
User can fill RAMs with plain or cipher data patterns, set encryption key, set tweakable key, IV and control test operation via serial console. When configuration is completed, AES256XTSdemo command menu will be displayed as shown in Figure 3‑1. The detailed information of each menu is described in topic 4.
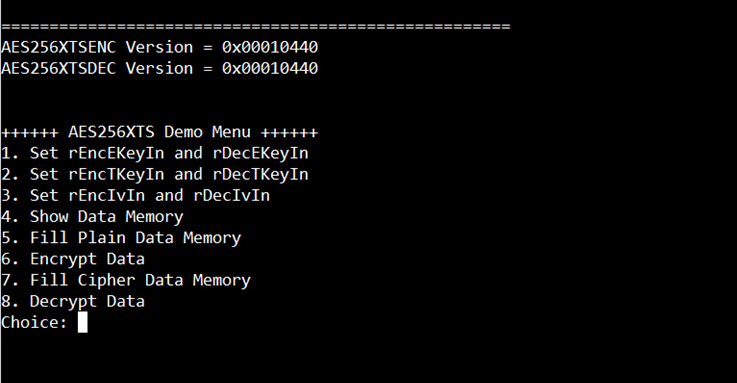
Figure 3‑1 Serial console
4 Command detail and testing result
Step to set encryption key as follows
a) Select “1. Set rEncEKeyIn and rDecEKeyIn”.
b) Current rEncEKeyIn will be displayed on serial console as shown in Figure 4‑1.
c) Set new rEncEKeyIn: User is allowed to input new key in hex format or press “enter” to skip setting new key. Then the current encryption key is printed again.
d) Current rDecEKeyIn key will be displayed on serial console.
e) Set new rDecEKeyIn key: User is allowed to input new key in hex format or press “enter” to use rEncEKeyIn as rDecEKeyIn. Then the current decryption key is printed again.
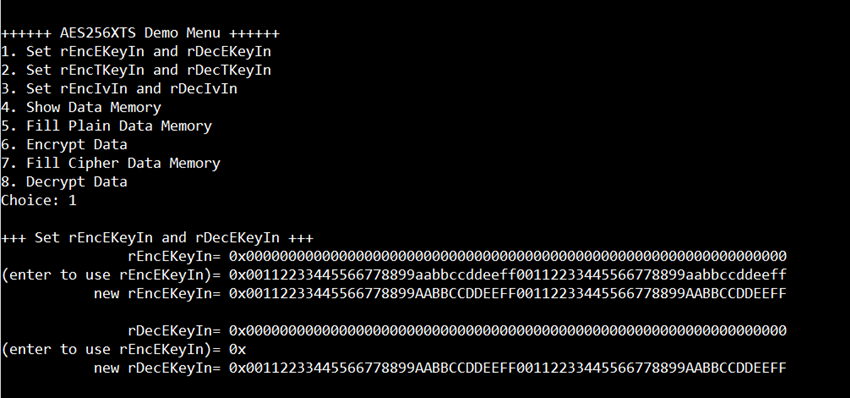
Figure 4‑1 Set rEncEKeyIn and rDecEKeyIn example
Step to set tweakable key as follows
a) Select “2. Set rEncTKeyIn and rDecTKeyIn”.
b) Current rEncTKeyIn will be displayed on serial console as shown in Figure 4‑2.
c) Set new rEncTKeyIn: User is allowed to input new key in hex format or press “enter” to skip setting new key. Then the current encryption key is printed again.
d) Current rDecTKeyIn will be displayed on serial console.
e) Set new rDecTKeyIn: User is allowed to input new key in hex format or press “enter” to use rEncTKeyIn as rDecTKeyIn. Then the current decryption key is printed again.
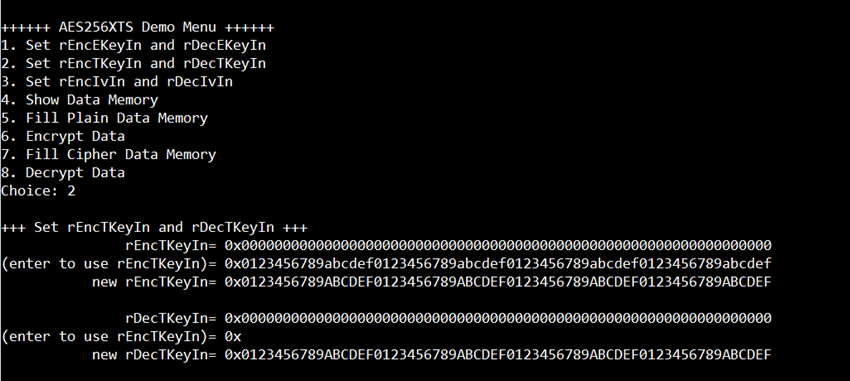
Figure 4‑2 Set rEncTKeyIn and rDecTKeyIn example
4.3 Set encryption/decryption IV
Step to Set encryption/decryption IV as follows
a) Select “3. Set rEncIvIn and rDecIvIn”.
b) Current rEncIvIn will be displayed on serial console as shown in Figure 4‑3.
c) Set new rEncIvIn: User is allowed to input new IV in hex format or press “enter” to skip setting new key. Then the current encryption IV is printed again.
d) Current rDecIvIn will be displayed on serial console.
e) Set new rDecIvIn: User is allowed to input new IV in hex format or press “enter” to use rEncIvIn as rDecIvIn. Then the current decryption IV is printed again.
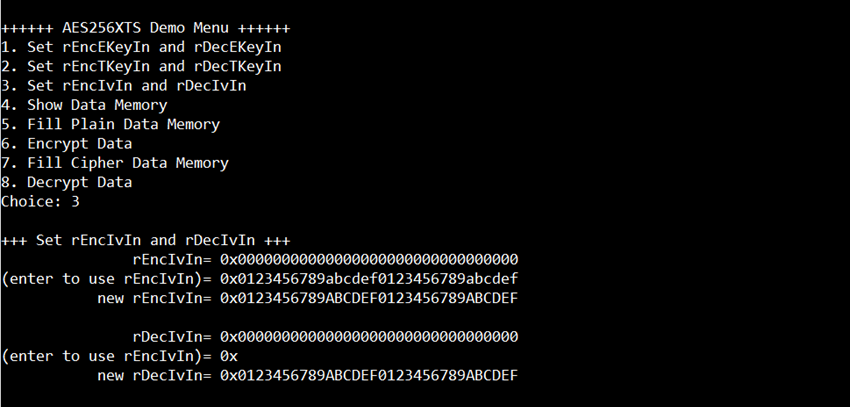
Figure 4‑3 Set rEncIvIn and rDecIvIn example
4.4 Show Data Memory
To show data in memory, user can select “4. Show Data Memory” and input the desired length of data in byte to show. Both plain data and cipher data will be displayed in table-form as shown in Figure 4‑4. User can press “enter” key to skip putting the number of data, then serial console will display 64 bytes (default value) of plain data and cipher data at address 0x0000-0x003F in four rows of table.
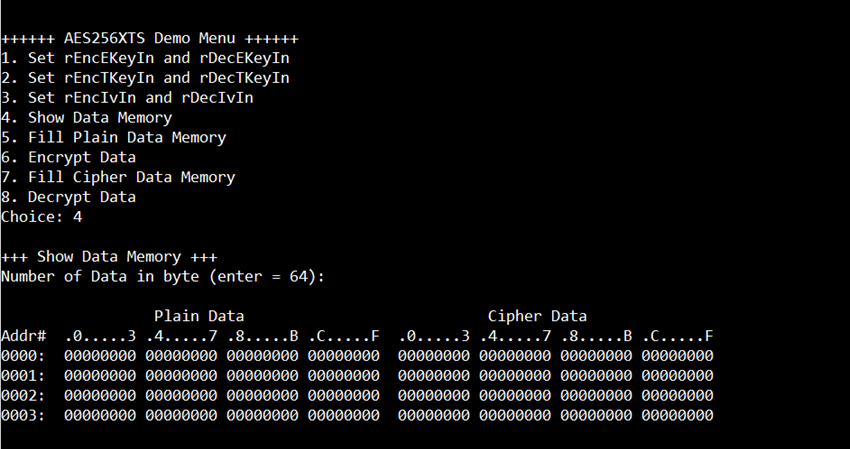
Figure 4‑4 Displayed Data example
4.5 Fill Plain Data Memory
Step to fill plain data in memory as follows
a) Select “5. Fill Plain Data Memory”.
b) Input the desired length of data in byte. User can press “enter” to encrypt 16 Byte plain data. user can select data pattern.
c) There are four pattern to fill memory.
a. zero pattern
b. 8-bit counter
c. 16-bit counter
d. 32-bit counter
d) Whole plain data memory is filled with selected data pattern.
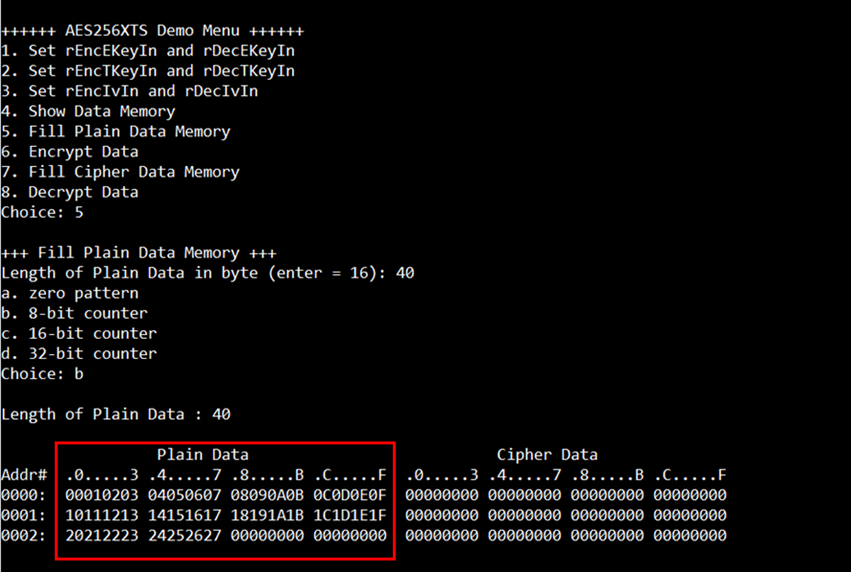
Figure 4‑5 Displayed Data when select pattern
4.6 Encrypt
Select “6. Encrypt” to encrypt plain data in memory. When the encryption process is finished, both plain data and cipher data will be displayed in table-form as shown in Figure 4‑6.
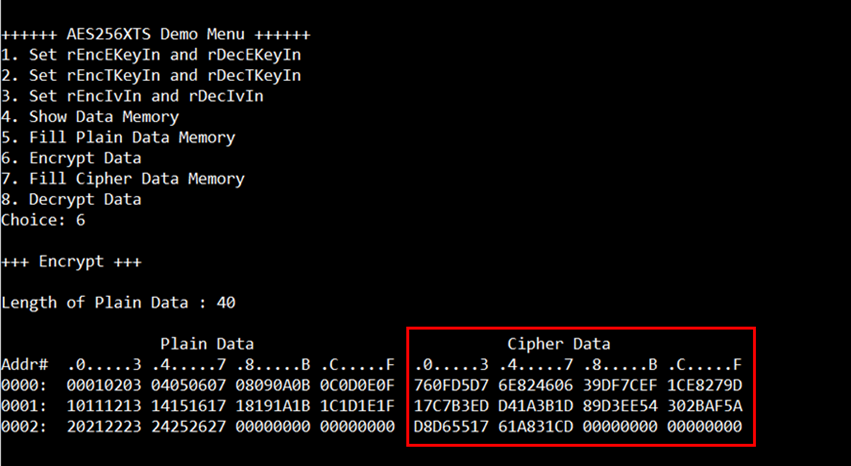
Figure 4‑6 Serial console after finished encryption process
4.7 Fill Cipher Data Memory
Step to fill Cipher data in memory as follows
a) Select “7. Fill Cipher Data Memory”.
b) Input the desired length of data in byte. User can press “enter” to decrypt 16 Byte Cipher data. user can select data pattern.
c) There are four pattern to fill memory.
a. zero pattern
b. 8-bit counter
c. 16-bit counter
d. 32-bit counter
d) Whole cipher data memory is filled with selected data pattern.
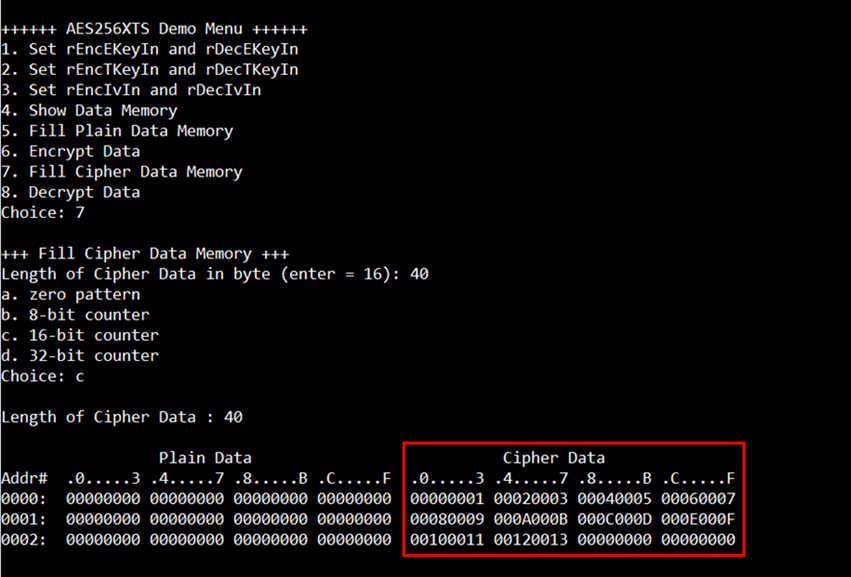
Figure 4‑7 Displayed Data when select pattern
4.8 Decrypt
Select “8. Decrypt Data” to decrypt cipher data in memory. When the decryption process is finished, both plain data and cipher data will be displayed in table-form as shown in Figure 4‑8.
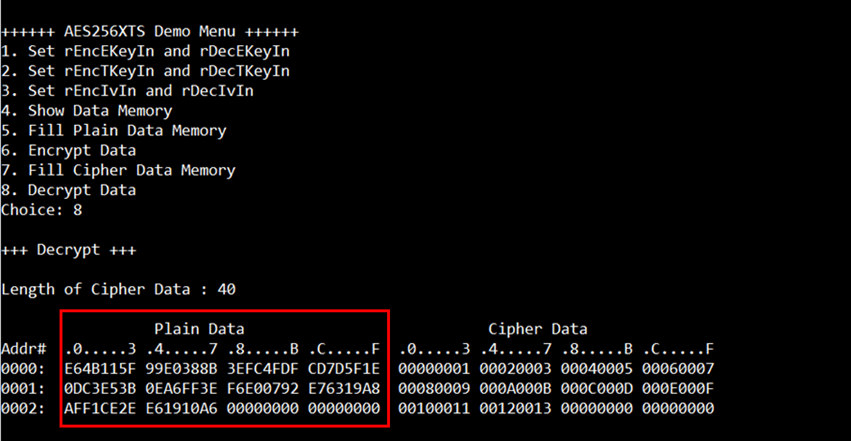
Figure 4‑8 Serial console after finished decryption process
5 Revision History
|
Revision |
Date |
Description |
|
1.00 |
30-Nov-2022 |
Initial version release |